I had heard about malicious actors potentially using the Right-To-Left-Override (Unicode U+202e) character a while back. This is the first time I’ve seen it for myself. The RTLO character tells the operating system to display the text following it in reverse order. So if a filename is called “thisisafile.doc.exe” with the RTLO character immediately before .doc, it would be displayed as “thisisafileexe.cod.”. While every application working with the file will recognize the file with its correct file extension, the way it’s displayed could trick the user into believing it is safe.
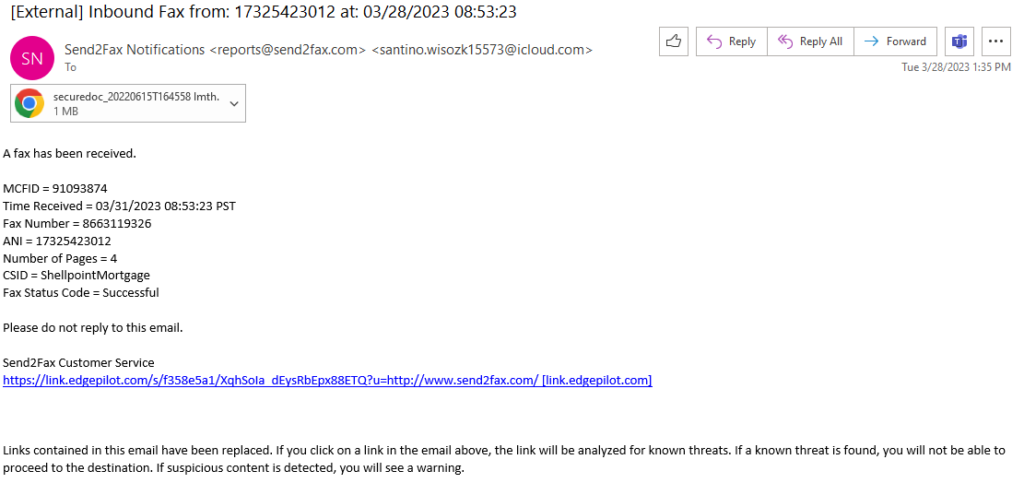
Here’s what the email looked like. Note the last line of the email regarding links in the email being replaced is exactly as the email arrived. This wasn’t added by the recipient email server.
Here are the (edited) email logs showing the email this file arrived as an attachment to.
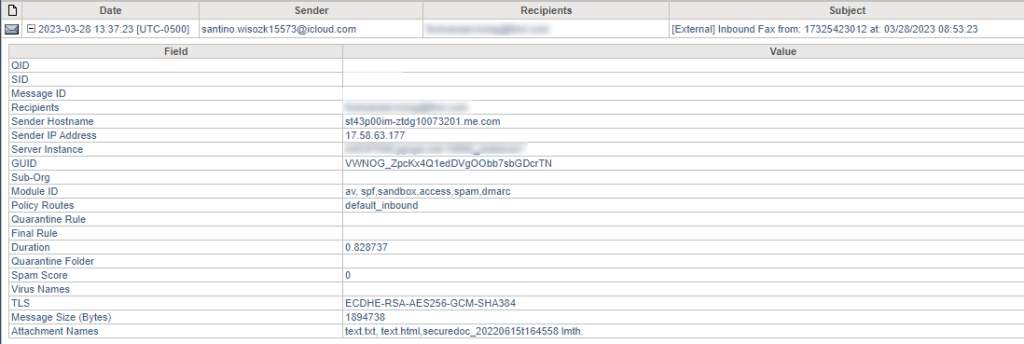
Note the last line showing the attachment name. This shows three attachments, text.txt and text.html, which are shown as attachments for virtually every email. The last filename is the interesting one. The logs show the file extension as “lmth.”. This is an html file with the RTLO character after the number 8.
Here is the file shown in Windows explorer:

You can see that Windows recognizes it as a “Chrome HTML Document”. Here’s what is looks like when you have file extensions displayed and go to rename the file:
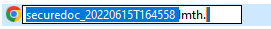
You can see it automatically selects the full filename except for the extension, including the RTLO character which shows as a space.
So the file is just an html file. It’s definitely malicious but the recipient should be happy that the first time an example of this character was found to be used in a malicious file, it was just an html file rather than an executable file. In this case, the file contained a script that decoded included text from base64 and wrote it to a file that displayed a Microsoft credential phish.

I recommend blocking all files with attachments containing this character. In the unlikely event a legitimate email arrives with a file containing this character, you can release it to the intended recipient. I really don’t see any legitimate emails would use this character in an attachment filename.
–Matt